Computing Threats
Don't take the bait! This page shows example computing threats, such as phishing scams, that you should avoid. Phishers are fishing for your personal information, such as passwords and credit card numbers. Never provide this information by replying or following links in the email. Under no circumstances will CUS or other members of the IT department ask for your password. If in doubt about the legitimacy of an email, contact CUS. To learn how to keep yourself protected, visit our phishing page.
To report a phishing scam you receive, email it (with full headers) to cus@reed.edu.
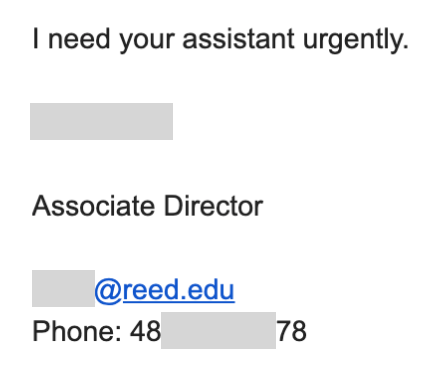
Spearphishing with phone number - Posted
This is a pretty standard phishing message. A short message with a sense of urgency, sent from a non-Reed address (<first.last><#>@example.com), impersonating a community member (name and title, even the correct email address listed in the body). In this case, the phone in the message signature is not the staff member's actual phone number.
The attacker is hoping that the recipient:
A) isn't paying close attention and replies to the "urgent" message, or
B) picks up the phone to verify that the message is legitimate, but uses the number included in the message instead of getting the number from a trusted source (i.e. the campus directory web page).
Stay safe! Be cautious! Use the campus directory if you're going to reach out to a community member by phone!
Give Me Access - Posted
Phishers and hackers are using more sophisticated social engineering techniques to lure their victims into giving away access, credentials or even buying them things!
Below is an example of such a complex attack. Glancing at the email, everything appears to be legtimiate: spoofing of the correct Reed address, few to no grammatical and spelling errors, and an almost believable request. What we can notice, however, is that they're trying to take conversation out of Reed's email system, as they want a response to an address outside of the organization. While this sometimes happens, albeit rare, any and all requests that come from a non-Reed email, or those that want us to redirect the conversation should be treated with high scrutiny. As always, if in doubt, the best way to verify a request is to give the person a call on their Reed phone, or compose a new email directly to them. No professor or staff member is going to ask you for an ebay gift card.
[Email]
From: RealReedAddress@reed.edu
Date: April 1, 2019 2:34:56 PM PDT
To: undisclosed-recipients;
Subject: Could I request X under my personal email address?Hello,
I am a professor of *department* and would like to have a *such and such* account to protect my password. I find nowhere to register, so I turn to you for help. You can contact me through my personal email (FirstNameOfPerson.reed.edu@protonmail.com) for better contacts.
Regards,
Real Name of Person at Reed
Title IX Phish - Posted
Title IX phish messages like the one below are targeting Reed and our peer institutions. Be wary of any email that directs you to take action of any kind (i.e., visit a website, login, or do something else) even if it's from a sender you recognize. If in doubt about the legitimacy of a message, contact CUS or the sender through a known, trusted method.Subject: Annual Title IX/VAWA Training
Good Morning,
It is time for the renewal of our Title IX/VAWA training. Please use the following instructions to complete the training. Every employee is required to complete this training within 24hrs. Once you have completed the training, please print your certificate.
Title IX/VAWA TrainingThese online training modules are offered through the Virtual Training Academy (VTA) On-Demand Tab.
The Title IX/Violence Against Women Act (VAWA) Training <link redacted> is designed to help you understand these important regulations and know how to appropriately respond to Title IX related incidents. This training is also offered through the Virtual Training Academy (VTA) On-Demand Tab.
To access the Title IX/VAWA Training, please visit the Virtual Training Academy at Virtual Training <link redacted> and log in with your username and password and enter your details:Link to tutorial to help you get started: <link redacted>
If you have completed the Title IX training last spring, you will use your same username (email) .
If you did not complete the training last year, click on the Register<link redacted> button.
After logging in, enter the code 08664f9b in the Add a Course box in the upper right-hand corner of the screen, then select Add.Thanks,
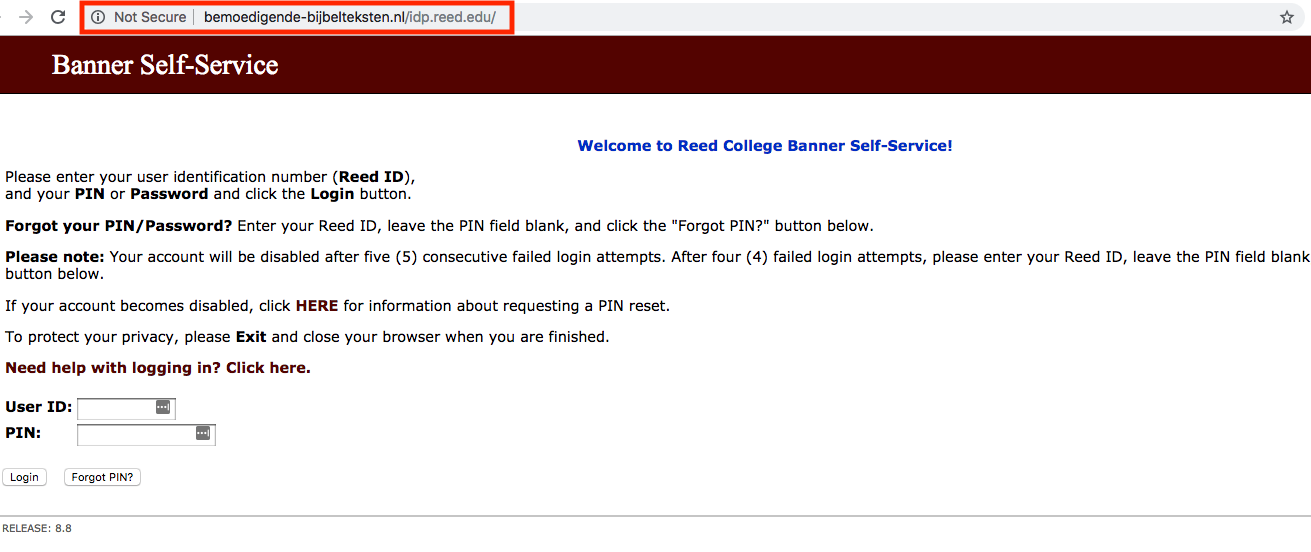
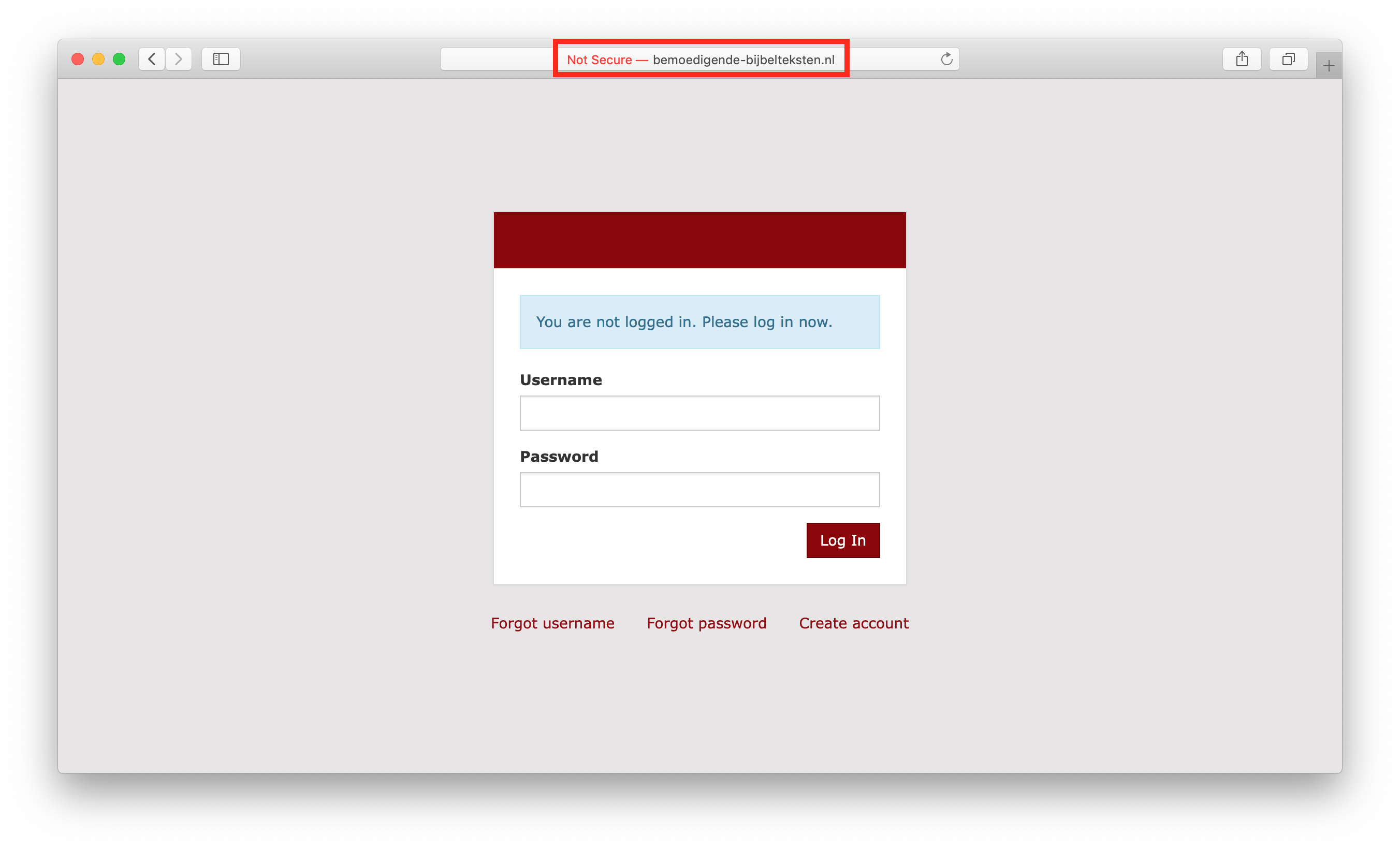
Spoofed Reed Login Website - Posted
A couple of different spear phish messages targeted hundreds of Reedies that led to fake Reed login pages. Without scrutinizing the URL, the web pages look identical to the legit ones. Please change your Kerberos and Banner web passwords immediately if you suspect entering your credentials on the bogus websites.
Subject: IMPORTANT UPDATE:- Please Read Immediately!! Date: Thu, 14 Feb 2019 08:50:26 -0800 From: Reed College - Alert <user@iit.edu> Dear: Students, faculty, and staff.You have important Health information from Reed College Health and Wellness Center. Please Click Here to read--
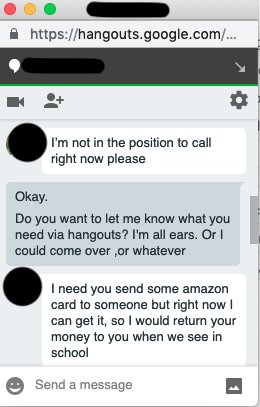
Google Hangout Phish - Posted
Spear phishers strike again! This time pretending to be a Reed employee (using a valid name and job title) on Google Hangouts! Be suspicious of any request no matter what communication method is used (email, chat, phone, text, etc.). Carefully examine the sender's contact info and please check with the Help Desk if in doubt.How to maintain this page ( IT staff only )